How to root an appliance
1. Root an Appliance
We often deal with appliances during our daily struggles. They provide a solution to a particular problem, and they come as a package. In the sense of administration, they usually offer management panels. You can't access the root account on these devices. Not being a superuser on a server I manage irritates us intensely. Having root means being able to operate the equipment after the warranty. First thing first, this operation means voiding your warranty. Be warned.
As the first victim of this series, We will start with a log related appliance. We won't share the model and make of this appliance. The appliance is bare-metal and runs on the Linux core.
To conquer an appliance, we need a working shell first. We started with the basic approach, grub has a limited but capable shell, and it can be exploited to get the root on the system. The appliance had a customized grub version that did not allow any edits. So we decided to attack directly to the filesystem.
2. Get a Shell
If BIOS access is possible, we can just run the device with a live CD and use chroot. This usually an option only for virtual appliances. Don't try to reset bios password on physical appliances unless you take the risk of turning it into an everyday server. Since BIOS was locked, we unplugged disk drives an plugged them to a testing server. When we tried to mount the drives:
mount /dev/sda1 /tmp/tmproot
mount: unknown filesystem type 'linux_raid_member'2.1 Rebuild the RAID
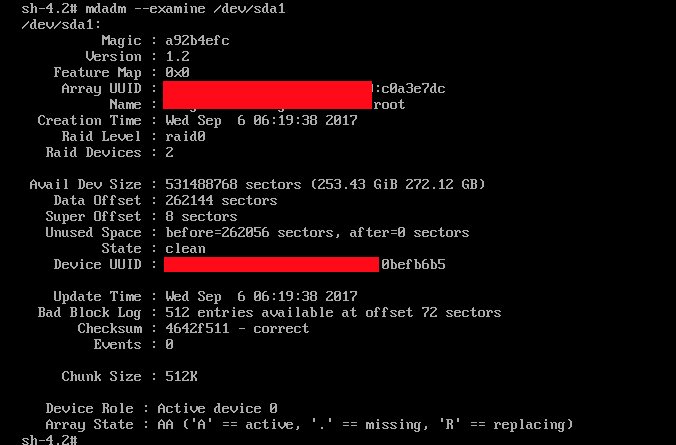
The partition belonged to software RAID managed by Linux. We analyzed the software raid to find out how to rebuild the RAID:
mdadm --examine /dev/sda1By parsing the information, we figured out the raid configuration. The following command could be used automagically to construct the RAID for you. With this command, mdadm will scan all the devices and assembles the raid if possible:
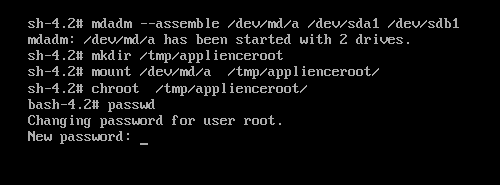
mdadm --assemble /dev/md/applienceraid --uuid yourraidUUID2.2 Get a Root Shell In Apllience
Chroot binary can give us temporary admin status on the device. To use the chroot, we need to mount the filesystem in a location you can read and write. When you run chroot command, you will get a new terminal which considers that directory as root. In that terminal, you can run the Linux command as you are typing in your appliance. Accessing the filesystem gets tricky for appliances.
Root login might be disabled from another configuration file, changing the root login shell can disturb the appliance configuration and might open vulnerabilities on the device. Just add a new user and give it sudo rights.